Address
155 Varsity Parade,
Varsity Lakes
QLd, 4227
Get in touch
1300 110 393
People and Vehicle Counting – Embedded within Avigilon Control Centre
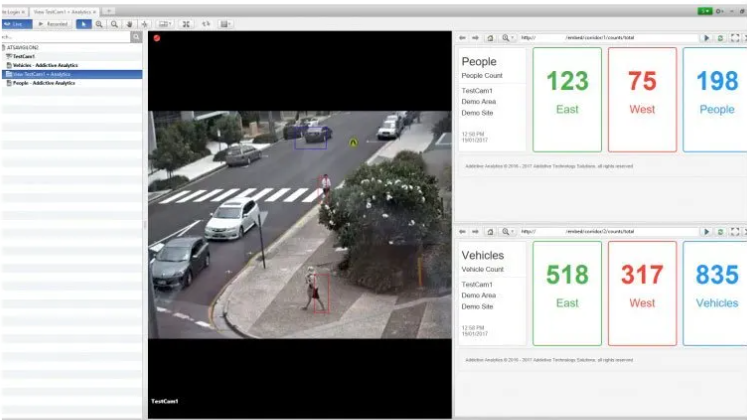
Embedded Analytics within Avigilon Control Centre Client
Addictive Technology Solutions
have developed another first for Video Analytics. We now have the ability to embed live People and Vehicle counting directly within the Avigilon Control Centre Client.
This integration allows for viewing counters in real time as well as recording the statistics for post use analysis and reporting. Counters can be embedded within any viewing window inside of ACC so that live streaming and analytics are presented at the same time.
This integration will prove extremely useful for a wide variety of monitoring applications.
To find out more or to have a demonstration of this technology, please email contact us
and we would be glad to arrange a demonstration.

By Robert Marsden
•
20 Dec, 2023
The global cost of a data breach last year was USD $4.45 million. This is an increase of 15% over three years. As we step into 2024, it’s crucial to be aware of emerging technology threats. Ones that could potentially disrupt and harm your business. Technology is evolving at a rapid pace. It’s bringing new opportunities and challenges for businesses and individuals alike. Not all technology is benign. Some innovations can pose serious threats to our digital security, privacy, and safety. In this article, we’ll highlight some emerging technology threats to be aware of in 2024 and beyond. Data Poisoning Attacks Data poisoning involves corrupting datasets used to train AI models. By injecting malicious data, attackers can skew algorithms’ outcomes. This could lead to incorrect decisions in critical sectors like healthcare or finance. Some actions are vital in countering this insidious threat. These include protecting training data integrity and implementing robust validation mechanisms. Businesses should use AI-generated data cautiously. It should be heavily augmented by human intelligence and data from other sources. 5G Network Vulnerabilities The widespread adoption of 5G technology introduces new attack surfaces. With an increased number of connected devices, the attack vector broadens. IoT devices, reliant on 5G networks, might become targets for cyberattacks. Securing these devices and implementing strong network protocols is imperative. Especially to prevent large-scale attacks. Ensure your business has a robust mobile device management strategy. Mobile is taking over much of the workload Organizations should properly track and manage how these devices access business data.
© 2024
All Rights Reserved | Addictive Technology Solutions Pty Ltd | Website Terms and Conditions | Privacy

